HP Exam HPE6-A84 Topic 9 Question 38 Discussion
Topic #: 9
Refer to the exhibit.
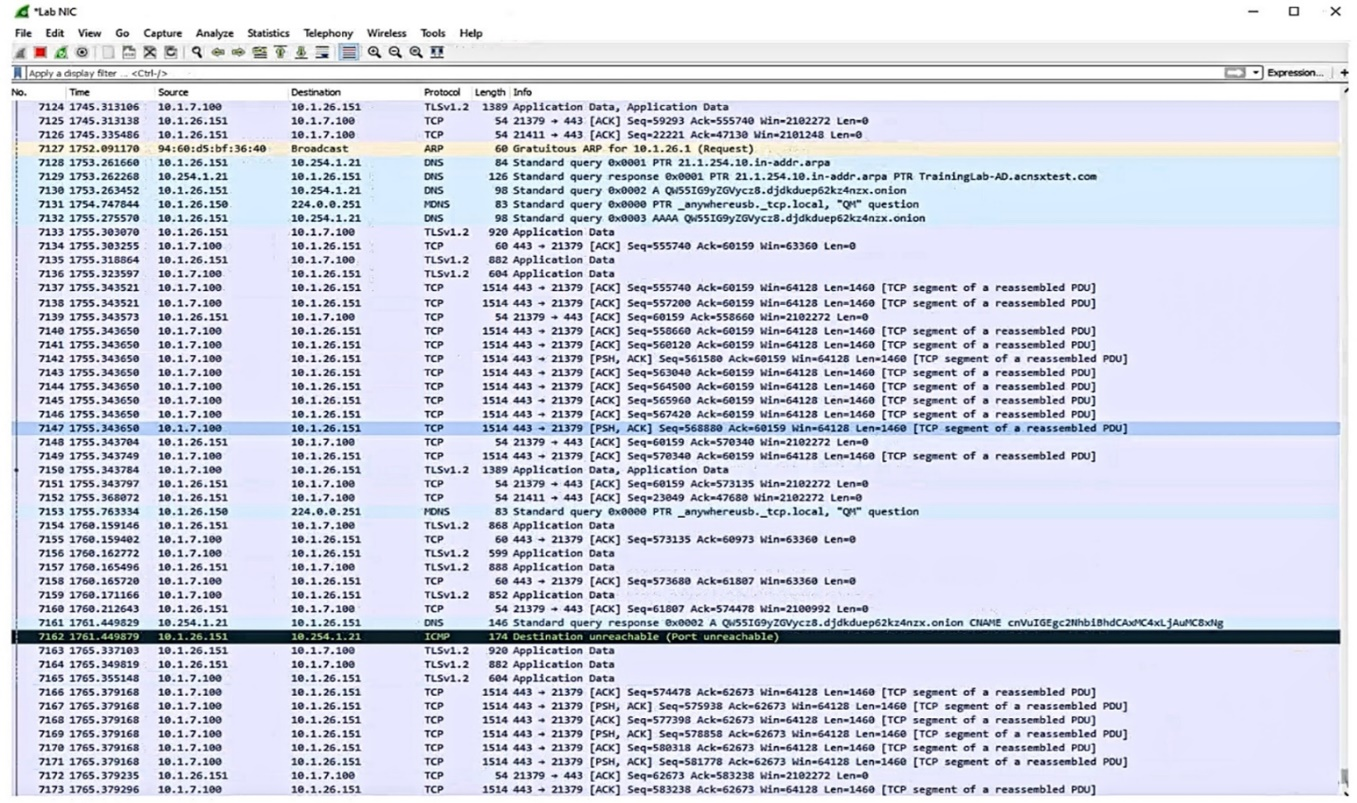
Which IP address should you record as a possibly compromised client?
This is because SNMPv3 is a secure version of SNMP that provides authentication, encryption, and access control for network management. SNMPv3-only is a configuration option on AOS-CX switches that disables SNMPv1 and SNMPv2c, which are insecure versions of SNMP that use plain text community strings for authentication. By setting the snmp-server settings to ''snmpv3-only'', the switch will only respond to SNMPv3 requests and reject any SNMPv1 or SNMPv2c requests, thus remedying the vulnerability and meeting the customer's requirements.
A) Enabling control plane policing to automatically drop SNMP GET requests. This is not a valid recommendation because control plane policing is a feature that protects the switch from denial-of-service (DoS) attacks by limiting the rate of traffic sent to the CPU. Control plane policing does not disable SNMPv1 or SNMPv2c, but rather applies a rate limit to all SNMP requests, regardless of the version. Moreover, control plane policing might also drop legitimate SNMP requests if they exceed the rate limit, which could affect the network management.
C) Adding an SNMP community with a long random name. This is not a valid recommendation because an SNMP community is a shared secret that acts as a password for accessing network devices using SNMPv1 or SNMPv2c. Adding an SNMP community with a long random name does not disable SNMPv1 or SNMPv2c, but rather creates another community string that can be used for authentication. Moreover, adding an SNMP community with a long random name does not improve the security of SNMPv1 or SNMPv2c, as the community string is still transmitted in plain text and can be intercepted by an attacker.
D) Enabling SNMPv3, which implicitly disables SNMPv1/v2. This is not a valid recommendation because enabling SNMPv3 does not implicitly disable SNMPv1 or SNMPv2c on AOS-CX switches. Enabling SNMPv3 only adds support for the secure version of SNMP, but does not remove support for the insecure versions. Therefore, enabling SNMPv3 alone does not remedy the vulnerability or meet the customer's requirements.
Shaun
2 months agoBroderick
9 days agoKerry
17 days agoBrynn
22 days agoMollie
29 days agoMagda
1 months agoGene
1 months agoFlo
2 months agoLavonna
2 months agoClay
2 months agoBrynn
16 days agoBrynn
1 months agoBrynn
2 months agoBilli
2 months ago