Eccouncil 312-96 Exam
- Topic 1: Single Topic
Free Eccouncil 312-96 Exam Actual Questions
The questions for 312-96 were last updated On Apr. 24, 2024
Which of the following method will you use in place of ex.printStackTrace() method to avoid printing stack trace on error?
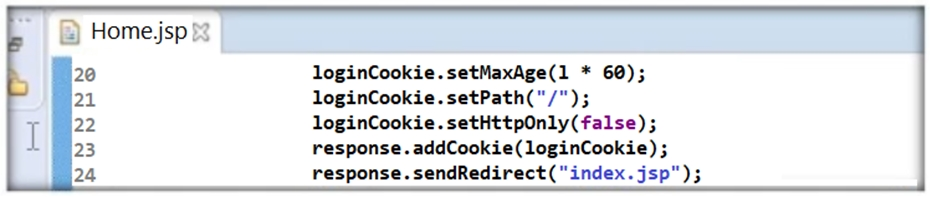
Thomas is not skilled in secure coding. He neither underwent secure coding training nor is aware of the consequences of insecure coding. One day, he wrote code as shown in the following screenshot. He passed 'false' parameter to setHttpOnly() method that may result in the existence of a certain type of vulnerability. Identify the attack that could exploit the vulnerability in the above case.
It is recommended that you should not use return, break, continue or throw statements in _________
The threat modeling phase where applications are decomposed and their entry points are reviewed from an attacker's perspective is known as ________
It is recommended that you should not use return, break, continue or throw statements in _________
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Currently there are no comments in this discussion, be the first to comment!