CompTIA PT0-002 Exam
- Topic 1: Single Topic
Free CompTIA PT0-002 Exam Actual Questions
The questions for PT0-002 were last updated On Apr. 25, 2024
After successfully compromising a remote host, a security consultant notices an endpoint protection software is running on the host. Which of the following commands would be
best for the consultant to use to terminate the protection software and its child processes?
The taskkill command is used in Windows to terminate tasks by process ID (PID) or image name (IM). The correct command to terminate a specified process and any child processes which were started by it uses the /T flag, and the /F flag is used to force terminate the process. Therefore, taskkill /PID <PID> /T /F is the correct syntax to terminate the endpoint protection software and its child processes.
The other options listed are either incorrect syntax or do not accomplish the task of terminating the child processes:
* /IM specifies the image name but is not necessary when using /PID.
* /S specifies the remote system to connect to and /U specifies the user context under which the command should execute, neither of which are relevant to terminating processes.
* There is no /P flag in the taskkill command.
During an engagement, a penetration tester was able to upload to a server a PHP file with the following content:
Which of the following commands should the penetration tester run to successfully achieve RCE?
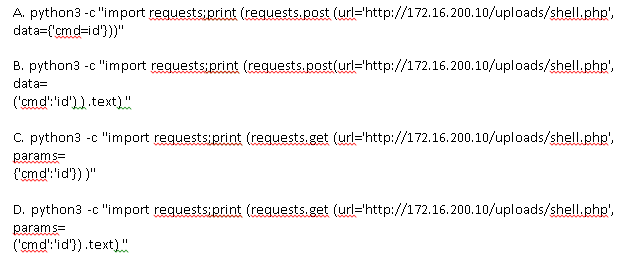
The PHP file uploaded by the penetration tester allows for Remote Code Execution (RCE) by executing the command supplied through the cmd POST parameter. To exploit this, the penetration tester needs to send a POST request to the PHP file with the command they want to execute.
Among the given options, Option A is the most suitable for achieving RCE:
It uses Python's requests library to send a POST request, which is appropriate because the PHP script expects data through the POST method.
The data parameter in the requests.post function is correctly formatted as a dictionary, which is the expected format for sending form data in POST requests. It includes the key cmd with the value id, which is a common command used to display the current user ID and group ID.
The only minor issue with Option A is that it prints the entire response object, which includes not just the response content but also metadata like status code and headers. To print just the response content (which would include the output of the id command), appending .text to the requests.post call would be more precise, but this is a small detail and does not affect the execution of the command.
The other options have various issues:
Option B is close but has a syntax error in the data argument. It uses parentheses () instead of curly braces {} for the dictionary, and also lacks the .text at the end to print the response content.
Options C and D use the requests.get method, which is not suitable in this scenario because the PHP script is expecting data through the POST method, not the GET method. Additionally, Option D has a syntax error similar to Option B.
Which of the following best explains why communication is a vital phase of a penetration test?
Communication is a vital phase of a penetration test to ensure all parties involved are aware of the test's progress, findings, and any potential impact on business operations. Discussing situational awareness involves sharing real-time insights about the security posture, any vulnerabilities found, and potential risks. This enables the organization to make informed decisions, mitigate risks promptly, and ensure the test aligns with business objectives and constraints.
Which of the following is the most common vulnerability associated with loT devices that are directly connected to the internet?
IoT devices are often shipped with default passwords, which are easily discoverable and widely known. Many users fail to change these default credentials, leaving the devices vulnerable to unauthorized access. This issue is one of the most common vulnerabilities associated with IoT devices connected directly to the internet. Attackers can exploit these default passwords to gain control over the devices, potentially leading to a range of malicious activities, including the recruitment of the devices into botnets for Distributed Denial of Service (DDoS) attacks, data breaches, or other cybercriminal activities.
A penetration tester is enumerating shares and receives the following output:
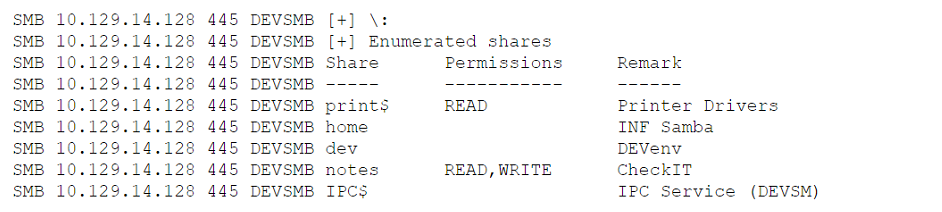
Which of the following should the penetration tester enumerate next?
The output displayed is typical of what one might see when using a tool like smbclient or enum4linux to list shared directories on a system that uses the SMB (Server Message Block) protocol. Here's a brief overview of the shared resources that have been found:
1. print$ - This share is generally used for printer drivers.
2. home - Could be a user's home directory, usually requires authentication.
3. dev - Suggests a development environment, possibly containing code, scripts, or tools that could be useful for further penetration.
4. notes - This has read and write permissions and could contain information such as user notes or documentation.
While all these shares could potentially provide valuable information, the dev share stands out for several reasons:
* Development Environment: As it seems to be a development share, it may contain scripts, tools, or code repositories which could be less secure than production environments and possibly contain sensitive information such as hardcoded credentials, configuration files, or backup files.
* Standard Names: Shares like print$ and home are common and are likely to be properly secured or to contain less sensitive information.
* Writable Share: The notes share is also interesting because it has read and write permissions, which could be exploited to upload malicious files or modify existing ones. However, the potential for finding exploitable material or sensitive information might be higher with the dev share.
In penetration testing, the goal is to find the path of least resistance that provides the highest potential for deeper access or sensitive information discovery. The dev share represents a target that could yield such information or further avenues for exploitation, making it the next logical step for enumeration.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Currently there are no comments in this discussion, be the first to comment!